End-user Security Awareness
Do you think your IT security setup is under control? Firewalls are in place, endpoint protection systems activated, your WiFi infrastructure is correctly secured, applications are updated with the latest patches and maybe you even had your infrastructure audited by a security specialist. Congratulations! Yet, know that your real security level is only about the weakest link: your end-users.
With our Security Awareness offerings, you systematically inform and test their awareness. This is crucial in preventing any security risk (hacking, crypto lockers, fraud, data theft, ...).

"Although 78% of people pretend they are aware of security risks, studies show that 63% of people still click on risky links"
(Source)
"You can secure your company as well as possible with all kinds of security software, but your employees always remain the weakest link in terms of IT security. You have to create a change in behavior and that' s not something that can be done overnight. With Easi we found a reliable partner to guide us in this."
Tristan Vingerhoets - Network and Security Engineer at Duvel Moortgat
Why is Security Awareness important?
Unknown attacks
Hackers are becoming more and more inventive and launch new techniques every day. Even though advanced security solutions offer a very high level of security, unknown attacks still remain an important risk for your IT environment.
Malicious applications
Seemingly legitimate applications performing malicious actions is a major risk if your end users are not well aware of the security risks involved. Employees think in good faith that they are installing a benign application, but in reality, they might be bringing in a virus.
Human errors
Humans are human, that's why errors happen. Hard-working and dedicated employees sooner or later make mistakes. A click on an attachment, a USB-stick inserted in a corporate device, a connection to a non-secured WiFi-network can be enough to make your network vulnerable to hackers.
Weak passwords
"password" and "123456789" are still among the most used passwords worldwide. If employees use weak passwords or use the same password on different accounts & services, that's a serious risk! Make them aware of that!
We quickly saw the positive results of the security trainings.
Our colleagues are more cautious and have quickly adopted the right reflexes to avoid falling into the traps of hackers.
Sabrina Corthout - Head of IT at Astara

Our Security awareness training approach
We pay a lot of attention to the intake we do with every customer individually. Security concerns are different for every company and are based on a lot of factors, like the activity sector, demographics of employees... We want to build an offer that responds to your specific pain points and that effectively tackles your questions/issues.
We don't build standard presentations or one-size-fits-all training programs but prefer an in-depth, detailed analysis of your situation which results in a qualitative approach. We will decide together on the content of the program as well as the format, to make sure the right and appropriate focus is put on the right topics.
A security awareness training program can take multiple forms, going form a one-shot, in-class training session, over an e-learning program, a repeated program that runs over several months until a "User Awareness as a Service" model where we pro-actively run regular awareness campaigns & tests throughout the year.
During this stage, we will perform the actions agreed on during the intake meeting. This can contain a lot of topics & actions like phishing campaigns, social engineering, training sessions, workshops, etc... Our ultimate goal is to make your employees aware of the importance of the topics listed below. That's why we foresee most of the time intermediate surveys and/or quizzes to measure the progression of your employees. Hereby a - non-exhaustive - list of things we can cover during this stage.
Phishing protection
- Anti-Phishing campaigns
- Avoiding Dangerous Attachments
- Avoiding Dangerous Links
- Data Entry Phishing
Passwords & Authentication
- Secure Passwords
- Password Management
- Password Policy
- Multi-Factor Authentication
- Identifying Compromised Accounts
Email security
- Email Protection Tools
- Email Security
- Email Security on Mobile Devices
- Spear Phishing Threats
- Social Engineering
Safer Web Browsing
- URL Training
- Safe Social Networks
- Protecting Against Ransomware
- Mobile App Security
- Travel Security
Data security
- Data Protection and destruction
- GDPR
After the execution of the project, we will report you with the evolution we see in the level of IT Security Awareness among your employees. The results of the performed actions and the sessions will be gathered, analysed, presented and discussed together. Based on the results, follow-up actions can be planned if needed.
Flexible offerings
In-class or e-learning
The choice is yours: our security awareness trainings are available in in-class format (in our offices or in your own offices) or via e-learning, or a mix of both methods. Together, we will determine the best methodology for your company.
One-shot or repeated
One-shot sessions are useful, but anyone knows that repetition is important when habits and behaviors have to be changed. That's why we also provide programs that run over a longer period of time. We are seeing significantly better awareness scores at customers that perform regular awareness campaigns.
Security Awareness as a Service
Our Security Awareness as a Service offering brings awareness trainings in a managed services model. By regularly and unexpectedly putting your employees to the test, on the one hand, and by continuing to emphasize the risks of phishing, on the other hand, your organization evolves towards a safer environment.
World-class partnership
We're working with Proofpoint, a top-notch security awareness provider that offer the most effective cybersecurity and compliance solutions to protect people on every channel including email, the web, the cloud, and social media.
Their tools help us managing phishing campaigns, assessments, e-learning modules & quizzes al along your security awareness journey, and return valuable insights in your companies awareness level and attention points.
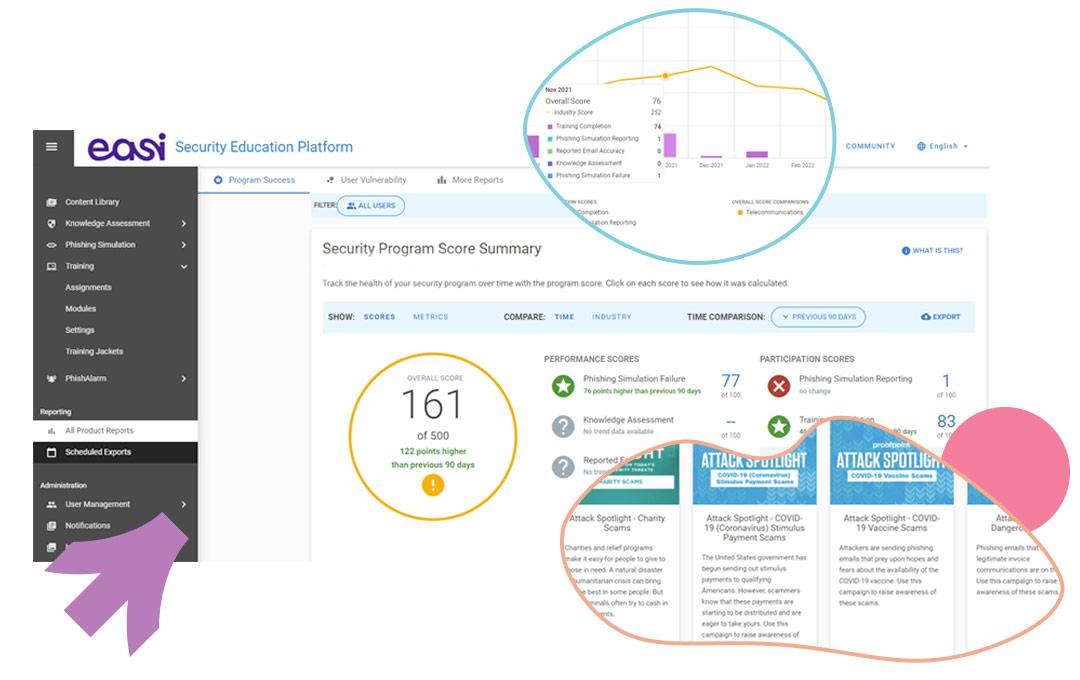
Over the years, this strong partnership has allowed us to build expertise that guarantees economies of scale, time savings and efficiency. In short, our personalized approach allows us to guarantee a certain ROI.
Maxime Lamarche - CISO at Easi