What is ISO 27001?
ISO 27001 is a globally recognized standard in the field of data protection. A company that obtains this certificate demonstrates that its organization, products or services meet a wide range of requirements in the field of the information security management system (ISMS). The certificate shows that the organization handles data well: personal data, financial data, intellectual property or data of third parties in general. To qualify for an ISO 27001 certificate, a company must comply with 114 controls (subject to exceptions that do not apply to the company). Whether these controls are met is determined by an external auditor (SGS, Deloitte, KPMG, ...) who issues the certificate if, after an audit, it appears that all standards are met.
Why ISO 27001?
An ISO 27001 certificate is a quality label that gives charisma to your organization. It gives confidence to prospects and customers about your respect for the GDPR legislation and the way your organization deals with data in general: a requirement that is more than justified by customers, new customers and governments. You don't achieve it just like that: it's a long but interesting process. It offers clout for commercial opportunities and also provides better internal guarantees towards business continuity. Companies with an ISO 27001 certificate are de facto strongly armed against data leaks. It does not offer 100% protection, but ensures that data security is the focus of attention of the entire organization.
ISO 27001 does not certify perfection, but excellence!
Unfortunately, perfection does not exist. You can always strive, always improve, but even for those with 99.9% security, a risk of 0.1% remains. Risks will always be there, that's why ISO does not require perfection. A report without comments is literally unseen during an audit.
Auditors will draw up a report with major or minor non-conformities. With major non-conformities you fail. These are fundamental changes you still have to make before you can obtain a certificate. Minor non-conformities are often isolated, smaller cases. As long as the auditor notices that you are reacting correctly and taking the right action, it is not a stumbling block.

To qualify for ISO 27001 certification, you must meet at least 90% of the 114 controls. We are happy to assist you in this respect. Guidance that is built up from your own expertise and will always differ due to your own in-house knowledge. You can read here how we approached this for our own company.
How can Easi help?
Tailor made guidance
Our advice will be shared very transparently and will always be tailored to your scope, business objectives and employees. You and your employees know your organization best: this, in combination with our expertise, ensures that we work in the most cost-efficient way.
At your own pace
We start each project tailored to your budget and always with your TCO in mind. Would you like to take care of some or all of the controls yourself? Then that's possible! You determine the pace and the investments you want to make, backed up by the right strategy we provide you with.
Certified ISO partner
Our experts are themselves "certified ISO Lead implementors". This ensures that we can meet your requirements and provide value-added support, using our industry insight and data protection expertise.
We lead by example
We apply our own approach to our own products and people. Indeed, Easi's cloud solutions and employees comply with the ISO 27001 standard. Everyone in our organization is effectively immersed in the ISO atmosphere every day. This ensures that ISO is always top-of-mind. Our internal always-on security awareness training program plays a major role in this.
Also if it has to go fast
Our approach ensures that the main pitfalls of the certification process are covered, which accelerates the process. The impact on your business operations and resources is minimized. If desired, we offer guidance from A to Z, from risk analysis to the implementation of corrective actions. If you hold someone internally responsible for this, we function as guides and sounding board.
Meet our CISO-as-a-Service
ISO 27001 action plan
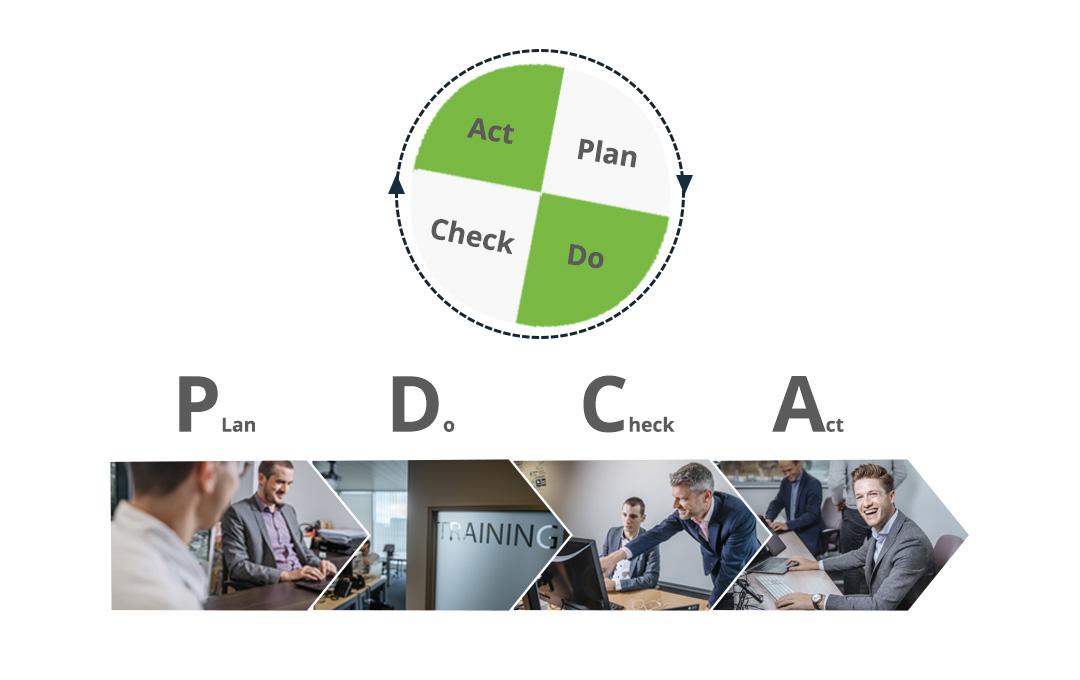
There is no one-size-fits-all approach to obtaining the certificate. We always start from the Plan-Do-Check-Act principle tailored to your structure: In step 1 we draw up the strategy together to obtain the certificate as efficiently as possible. Based on your input we determine the scope and match it with the objectives you have in mind. Throughout the entire process leadership is central: certain points of the checklist remain in your own hands and you finish under your own leadership, other points we do together, and other points we can fully take care of. Next to determining the scope we also do in step 1:
- a baseline measurement (online and offline)
- risk analysis of current data security
- starting the thinking process around the control program
- determine how the security ISMS will be controlled
- drawing up a security plan
As the word says, in this phase we are going to execute the plans made in advance. Implementation of the ISMS and training are the most important issues here. An ISO 27001 certificate can only be obtained if the management can demonstrate that it makes an effort to inform all those involved and to teach them how to deal with data security both on and offline. As already mentioned, our user awareness training courses are ideal for this. What are we still doing in this phase?
- measurement and reporting
- incident reporting
- setup of the ISMS
In this phase we proceed to an internal audit, with the aim of checking whether the measures taken meet the requirements of ISO 27001. The efficiency and effectiveness of the ISMS is assessed. On the basis of this audit, the management will make decisions about preventive and improvement actions. The internal audit team is quite independent in making these recommendations.
The next step is an external audit: this is carried out by one of the certification bodies. They determine whether you do indeed meet the standards. We can put you in contact with the appropriate organization based on your scope.
We also provide:
- additional checks and reporting
- Provide a declaration of applicability about ISO 27001
We ensure that any corrective actions are planned and carried out after verification by the external party. A continuous process also requires improvement actions. Hackers do not stand still and the standard demands to foresee improvement actions. You can also contact us for this.
