What is penetration testing?
Penetration testing, pentesting or a pen test is a well-intentioned attempt to hack your company, application or business systems.
How is penetration testing "well-intentioned" hacking?
The purpose of a penetration test is to expose IT vulnerabilities without exploiting them. Companies use the insights from penetration tests to improve their security posture.

Why does my company need a penetration test?
Knowing your vulnerabilities and how attackers like cybercriminals can use them, is one of the best insights you can have into improving your IT security posture.
It is important to know that such vulnerabilities can really be found in all layers and facets of your business:
IT Networks
Wifi, LAN, WAN and VPN connections, routers, devices, etc.
Business apps & systems
Your ERP, CRM or other business application, as well as business processes
Configurations
The configuration of firewalls, cloud access, enterprise software, in short, your layer of protection against cybercrime.
Your employees
Physical access to your offices or your business devices, yes even the comings and goings of your employees
Hackers usually conduct a thorough investigation before they strike, and that's how ethical hackers operate as well.
Are you ready for a penetration test?
How does a penetration test work?
Penetration testing can be done in a variety of ways, and that's because there are always a lot of factors that ensure that no two situations are the same.
For example, every company is unique: every IT infrastructure (applications, networks, etc.) looks different and is secured differently on top of that. This means that penetration testing is not a ready-made solution. Or is it? There are some processes that keep coming back.
What follows is a penetration testing step-by-step guide
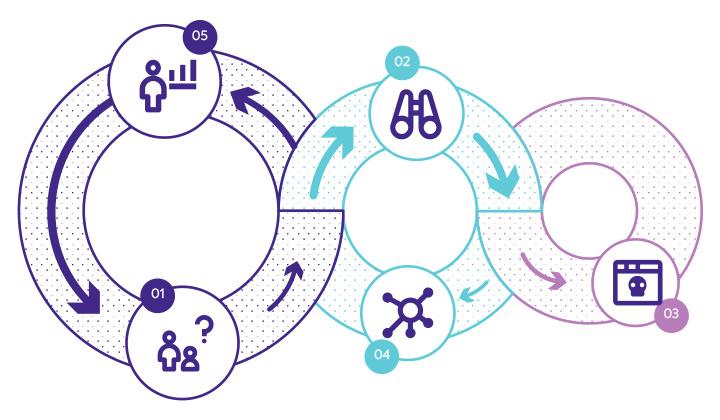
In the first phase, you're going to determine the scope of the penetration test. What do I really want to know? Theoretically, this is your research question.
Such a research question might be:
"Is my web application secure?"
"Is my business data sufficiently protected?"
"Are my business applications properly configured in terms of roles and permissions?"
To get a better overview of the scope of the penetration test, it is best to set up the research question in consultation with the different stakeholders of the penetration test. Based on that research question you can define the goal or goals of the penetration test, as well as the systems and test methods that will be used (more on that later).
To better understand those systems, the pen testers are going to try to find out already valuable information such as networks, domain names, mail servers, etc. In this way, they can find out a lot of possible vulnerabilities relatively easily.
As already indicated, cybercriminals will often prepare well before they strike. During the penetration testing process, it is no different. In this step, the pen testers try to understand how your systems would react during different intrusion attempts.
They do this by using automated tools, but mostly by making smart use of the Internet.
They check the code of the various business systems for bugs or possible security gaps, which may or may not be indicated online. In addition, they often perform a vulnerability scan to look for old or unpatched components that may be vulnerable to known exploits.
Based on what the pentesters have learned from the previous penetration testing phases, the weak points in the target's systems will now be used to penetrate.
How they do this depends on a case-by-case basis; they may use brute force, SQL injection, cross-site scripting, retrieve passwords through poorly secured authentication, or deliver malware through social engineering practices.
The possibilities are endless, but the difficulty is going unnoticed by the company's security systems.
The goal of this phase is to gain a lasting advantage from the attack. The attackers (in this case with no malicious intent) are going to try to move laterally in order to discover sensitive assets and gain persistent presence - long enough for cybercriminals to gain in-depth access to your systems.
This is the key phase of penetration testing, the pen testers now build their "file" by imitating APTs (advanced persistent threats). In this way, they stay under the radar (days, weeks, months) just long enough to obtain enough sensitive information, which they will analyze and later present, after which improvements can be made.
Remember: Pentesters are good boys and girls. Their purpose is not to do harm, but just to make companies aware of possible vulnerabilities and possibly fix them.
Everything they learned during the entire penetration testing process is written up in a detailed report:
- The specific vulnerabilities found and used or not used
- How access was gained and in what other possible ways it could also be gained
- Which systems were compromised
- Whether and when they were detected and how they were responded to
- Etc.
This report should enable the security team or IT team (or your service provider) to configure security systems and apply security solutions as needed.





.png)