What are Ethical Hackers?
Or rather, who are Ethical Hackers, because that's what you call the "good cybercriminals" who attack your company. They know all the tricks of the trade and use all the tools a real hacker would use.
Here's a sneak peek at these intriguing and mysterious members of our security team. (Spoiler: not all hackers wear hoodies!)
What is the difference between ethical hackers and malicious hackers?
The difference is clearly already in the name. Malicious hackers have malicious intentions: stealing data or money, or just taking down servers for fun. Ethical hackers, on the other hand, will try to crack your systems with your own permission, to make your company aware of the weaknesses in your IT security.

The purpose of such a penetration test is to obtain a clear analysis of the security posture of your company.
A well-developed penetration test service will also provide a step-by-step plan for how you can efficiently solve the weak spots in your cyber defense.
How does an Ethical Hacking process work?
Often hackers prepare well before they strike. That's what our Ethical Hackers do too.
They try to find out as much as possible about your company, company structure, employees, IT infrastructure, etc. after which they strike ruthlessly. Or do they? Our Ethical Hackers proceed as follows:
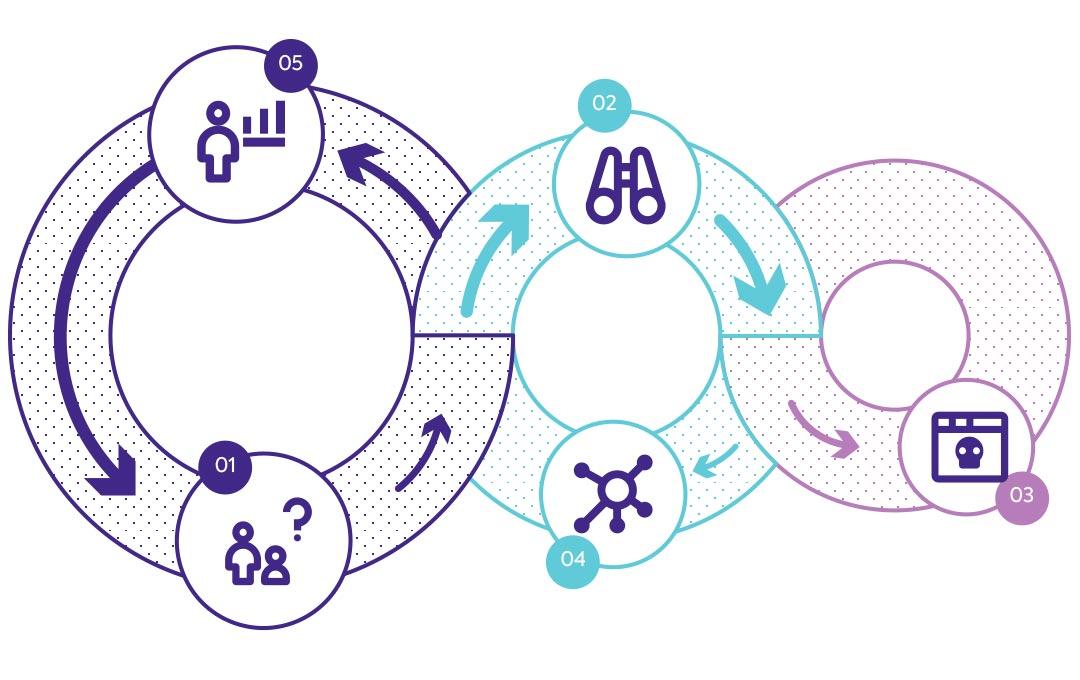
1. Planning & reconnaissance
The playing field is defined. Together, we draw up the research question and agree on the limits of what is allowed during the ethical hacking process.
2. Scanning
Our Ethical Hackers prepare by examining your IT infrastructure, systems and business processes.
3. Penetration
Our Ethical Hackers will use a thorough analysis and will try to hack your security systems while staying undetected.
4. Maintain access
Trying to remain undetected is now the objective, or at least long enough to obtain sensitive information.
5. Analyse
Ethical Hackers provide you with a detailed analysis and with possible solutions to prevent breaches.
Certified Ethical Hackers
An ethical hacking process is best performed by certified Ethcial Hackers. They are best placed to simulate a real-world attack.
For this they have acquired knowledge about malicious practices and also tested this knowledge by obtaining various certificates or testing it during hacking competitions.

Our Ethical Hackers are all multiple certified in various fields, but their IT experience is not the reason we hired them.
No, they were hired because they were all real White Hats (good knights, or knights on the white horse if you still believe in fairy tales) who simply know a lot about bad things.
For example, one moment you may be chatting pleasantly with them and two seconds later your badge is copied giving access to sensitive data.
In addition to learning their skills at school, they have mainly expanded their knowledge themselves through hands-on experimentation and participation in hacking competitions. They are all hackers with a good side. Our open corporate culture allows them to fully indulge in what they are good at.
Clients appreciate this way of working as well because of our out-of-the-box thinkers who leave no question unanswered.












.png)